Alberto Baban's Email & Phone Number
Presidente VeNetWork S.p.a.
Alberto Baban Email Addresses
Alberto Baban Phone Numbers
Alberto Baban's Work Experience

Venetronic Srl
Co Owner
April 2013 to Present

ATEX Industries S.p.a.
Co Owner
January 2012 to Present

GTA moda S.p.a.
Owner
January 2014 to Present

Fantic Motor S.r.l.
Co Owner, Board member
October 2014 to Present

UNICEF Italia
Board Member
October 2014 to Present

TREVISAN SRL
Co-Owner
September 2015 to Present

VeniceByBoat
Co-Owner
August 2016 to Present

Antica locanda dalla "Zanze" . Venezia
Investor
May 2017 to Present


Bellelli srl
Co-owner
June 2019 to Present

Officine Minute srl - STRAHL - Grain Dryers
Owner
February 2020 to Present

Trisottica srl
Co-Owner
October 2020 to Present

MOTORI MINARELLI SPA
Board member Co-Owner
January 2021 to Present

A&T - Automation & Testing
Presidente Comitato Scientifico
June 2019 to Present

Agrimec srl
Owner
July 2019 to Present


Italtronic srl
Owner
October 2018 to Present

VeNetWork S.p.a.
Presidente
May 2011 to Present

Maschio Aratri
Owner
April 2017 to July 2020

Venetex
Co-owner
April 2016 to September 2019

Milanobike
Co-owner
February 2016 to December 2018

UNLIMITED JEANS
Co-Owner
July 2016 to April 2018

VNT Medical
Co Owner
January 2014 to January 2018

Leaf S.p.a.
Co Owner
January 2013 to November 2017

Confindustria
Presidente Piccola Industria
November 2013 to November 2017

Confindustria
Vice Presidente
November 2013 to November 2017

Bluewago (acquired by Venetwork)
Co-owner
February 2015 to March 2017


Confindustria Veneto
Presidente Piccola Industria
November 2011 to November 2013
Show more
Show less
Frequently Asked Questions about Alberto Baban
What is Alberto Baban email address?
Email Alberto Baban at [email protected] and [email protected]. This email is the most updated Alberto Baban's email found in 2024.
What is Alberto Baban phone number?
Alberto Baban phone number is +39-049-5797300.
How to contact Alberto Baban?
To contact Alberto Baban send an email to [email protected] or [email protected]. If you want to call Alberto Baban try calling on +39-049-5797300.
What company does Alberto Baban work for?
Alberto Baban works for VeNetWork S.p.a.
What is Alberto Baban's role at VeNetWork S.p.a.?
Alberto Baban is Presidente
What industry does Alberto Baban work in?
Alberto Baban works in the Packaging & Containers industry.
Alberto Baban Email Addresses
Alberto Baban Phone Numbers
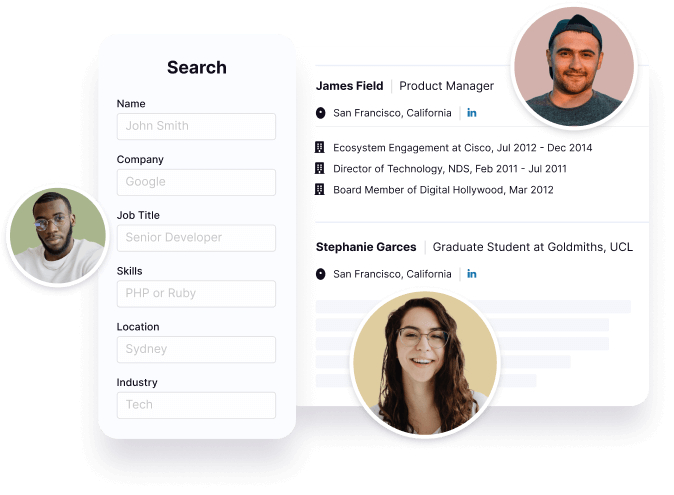
Find emails and phone numbers for 300M professionals.
Search by name, job titles, seniority, skills, location, company name, industry, company size, revenue, and other 20+ data points to reach the right people you need. Get triple-verified contact details in one-click.In a nutshell
Alberto Baban's Personality Type
Extraversion (E), Intuition (N), Feeling (F), Judging (J)
Average Tenure
2 year(s), 0 month(s)
Alberto Baban's Willingness to Change Jobs
Unlikely
Likely
Open to opportunity?
There's 97% chance that Alberto Baban is seeking for new opportunities

































Alberto Baban's Social Media Links
/in/alberto-baban-853a3a13